From time to time, I have to attempt an explanation to a marketeer as to why email blasts are an exercise in futility. But, knowing that they are happy with a 1% to 3% success rate with direct mail marketing, I realize that I am not speaking to the choir.
Many, many companies worth their salt have set their filters to deny image files. Generally, it is a bandwidth issue but here is a good example of it being a security issue, thanks to the intrusiveness of ContactMonkey…
From Ars Technica, by Sean Gallagher…
The funny thing is that C|NET also reviewed the software but went the other way and gave it a glowing review. My guess is that Jason Cipriani wasn’t fully aware of the software’s implications.
===================
The spy in your inbox
One PR company—and its tracking program—creep out an Ars writer.
by Sean Gallagher – Nov 6 2012, 4:10pm EST
Everything on the Internet is monitored in some way. Companies track what you do at work through deep packet inspection to make sure you don’t wander into territory forbidden by company policy, or dump corporate data to a remote server just before you give notice. The Web pages you visit and the HTML-based mass e-mails you open are logged and tracked by advertisers and marketers. And your boss can tell if you’ve ever opened that urgent message or not.
But people usually don’t throw it in your face and shatter whatever remaining illusions of privacy you might have, as someone did to my colleague Andrew Cunningham today.”Oh, man, a PR person was just totally creepy at me,” he interjected over IRC this morning.
The “creepy” was an e-mail that a media representative for a company called ContactMonkey sent on the heels of another one Cunningham had just opened. The second message included information about his location, the e-mail client he had used to open it, and the exact time it had been opened.
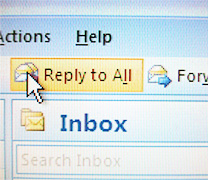
The Outlook plug-in toolbar for ContactMonkey’s Bridge.
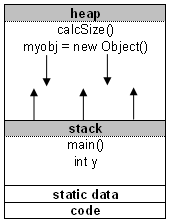
The message and the data were a demonstration of Bridge, a $5-a-month service that installs a plugin for Microsoft’s Outlook 2010 mail client and for Google’s Chrome browser for use with GMail. Bridge gives anyone the power to know those details for any message they send—or at least any message that lands in the inbox of someone who trustingly opens e-mails without blocking HTML-embedded images.
Invisible sprites
That’s because Bridge uses an embedded graphic with a unique Web address to track each message. That Web address includes calls to ContactMonkey’s tracker API, which include a message identifier and the e-mail address of the sender. When the recipient opens a tracked e-mail, it sends a secure Web request back to ContactMonkey’s server identifying the message, and the server records the IP address that the message was opened from and the date and time. Then it pushes back data to the sender, including how many times the message was viewed, the geographic location it was viewed at (based on the IP address), and the type of client it was viewed from (based on what the mail client reports as its type when it makes the HTML request).
The HTML code that embeds the tracking graphic in Bridge-bugged email messages (address of sender obscured).
Using graphics to collect metrics is an old hack, going back to the “sprites” used on many early personal Web pages to track page views. Web request based tracking is also heavily used by both legitimate large-scale e-mailers and spam factories to collect information such as when and where e-mails are opened, and to test the “hit rate” for various subject lines and offer teases.
But ContactMonkey gets even more personal about it, because it identifies each recipient explicitly, and reports back directly on them. It’s a technique akin to those used by some “spear-phishing” attacks to inject code into e-mails—no, it doesn’t execute code on the client. But it does create a way to collect information that might be useful for stalking someone.
Sweeping for bugs
There’s an easy way to block this sort of tracking with most mail clients. Microsoft Outlook, for example, will allow users to block embedded graphics in e-mails from all sources, or only display them in e-mails from sources in the user’s contact list. Most companies will set their mail systems to block HTML-embedded objects in messages for security purposes.
Users of Apple’s Mail app have a little less fine-grain control—unchecking “Display remote images in HTML messages” in Mail’s “Viewing” preferences blocks all HTML-embedded images from loading when you open a message. But that’s not the case with some mobile and Web-based mail clients—the iOS Mail app and Android 4’s built-in mail client, for example, both open HTML enclosures by default. That means if you open a bugged e-mail from a mobile device, the sender will be able to get information on where you are based on whatever IP address gets associated with your phone or tablet, whether it’s via Wi-Fi or your cellular provider.
If you do get tracked and discover it, however, there are some interesting ways to disrupt the tracking. For example, you could clip the tracking tag from the email and post it as a graphic or link on a website.
But that something like Bridge can be so easily blocked, and that it takes advantage of technologies that most business users may consider to be a security threat, should be enough to discourage most legitimate users from trying to use the service. After all, it’s really just a sneaky way of doing the same thing that a Return-Receipt-To e-mail header does, without giving the recipient a choice. And very few legitimate mass-mailers generate their e-mails from Outlook or GMail.
So that makes Bridge the provenance of a very narrow strip of users, one that includes stalkers, private investigators, ex-spouses and high-pressure salespeople—and the occasional public relations consultant.